High-speed networking has become a cornerstone of modern communication, enabling rapid data transfer and seamless connectivity across various platforms. As the digital landscape evolves, the demand for faster and more reliable networks has surged, driven by the proliferation of data-intensive applications, cloud services, and the Internet of Things (IoT). High-speed networking encompasses a range of […]
The landscape of information technology (IT) is undergoing a profound transformation, driven by the rapid advancements in artificial intelligence (AI) and automation technologies. These innovations are not merely trends; they represent a fundamental shift in how organizations operate, manage their resources, and deliver services. AI encompasses a range of technologies, including machine learning, natural language […]
The shift to remote work has transformed the landscape of modern employment, offering flexibility and convenience. However, this transition has also introduced a myriad of security risks that organizations must navigate. One of the most pressing concerns is the increased vulnerability to cyberattacks. Remote workers often connect to unsecured networks, such as public Wi-Fi in […]
Business continuity refers to the processes and procedures that organizations put in place to ensure that essential functions can continue during and after a disaster or disruption. This concept encompasses a wide range of activities, from risk assessment and mitigation strategies to recovery plans that enable a business to resume operations swiftly. Backup solutions, on […]
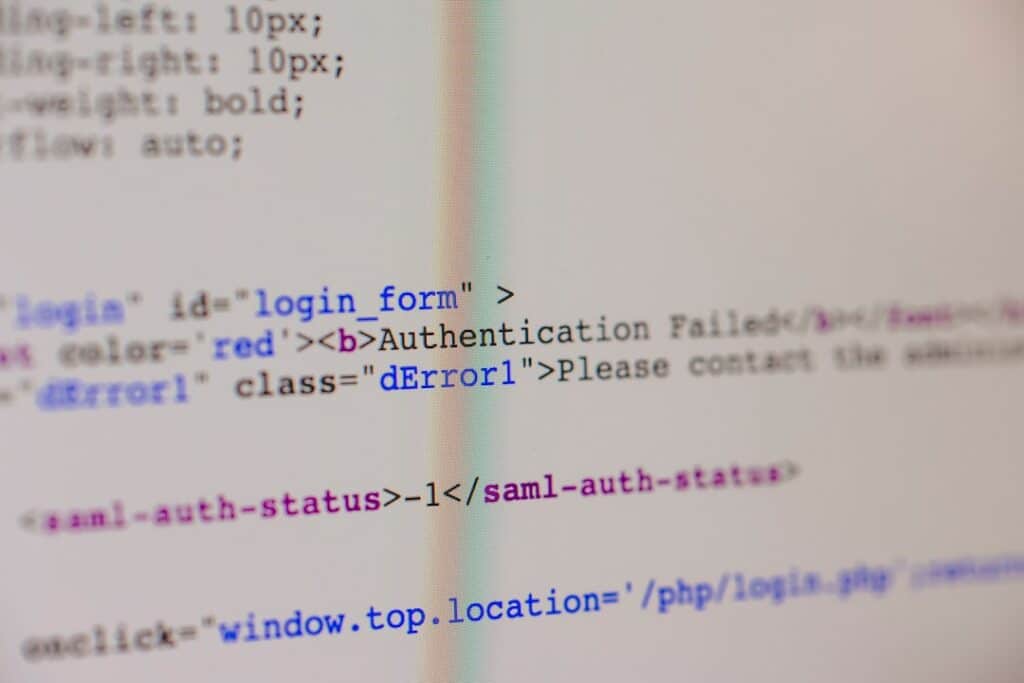
In the realm of technology, troubleshooting serves as a fundamental skill that empowers users to resolve issues that arise with their devices and systems. Whether it’s a malfunctioning computer, a smartphone that won’t connect to Wi-Fi, or software that crashes unexpectedly, understanding the basics of troubleshooting can save time, reduce frustration, and enhance overall productivity. […]
In the digital age, the threat landscape is constantly evolving, presenting organizations with a myriad of challenges. Cyber threats can range from sophisticated attacks by state-sponsored actors to opportunistic scams targeting unsuspecting individuals. Ransomware, phishing, and advanced persistent threats (APTs) are just a few examples of the tactics employed by cybercriminals. The increasing interconnectivity of […]
The distinction between cloud computing and on-premises solutions is foundational to modern IT infrastructure. Cloud computing refers to the delivery of computing services over the internet, allowing users to access resources such as storage, processing power, and applications remotely. This model is characterized by its flexibility, scalability, and the ability to pay for only what […]
The emergence of non-fungible tokens (NFTs) in the art world marked a significant shift in how digital art is created, bought, and sold. NFTs are unique digital assets verified using blockchain technology, which ensures their authenticity and ownership. This innovation allowed artists to tokenize their work, providing a new avenue for monetization that was previously […]
Deepfakes represent a significant advancement in artificial intelligence and machine learning, particularly in the realm of image and video manipulation. At their core, deepfakes utilize generative adversarial networks (GANs) to create hyper-realistic videos that can convincingly depict individuals saying or doing things they never actually did. This technology leverages vast datasets of images and videos […]
North Korea has emerged as a formidable player in the realm of cybercrime, leveraging its technological capabilities to engage in sophisticated cyber theft operations. The country, often characterized by its isolation and stringent control over information, has developed a cyber warfare strategy that is both aggressive and innovative. This strategy is not merely a byproduct […]